Insider threats are no longer a niche concern reserved for high-security environments. They span accidental data leaks, negligent practices, and deliberate exfiltration by trusted users. As organizations pour resources into Data Loss Prevention (DLP) solutions, questions persist about whether these tools can keep pace with evolving workflows, cloud adoption, and the human factors that create risk.
Why insider threats are uniquely challenging
Insider threats differ from external attacks in a critical way: the actor often has legitimate access to sensitive systems and information. That access can make it difficult to distinguish normal business activity from malicious intent. Traditional perimeter defenses are ineffective against insiders because the malicious actions originate from within trusted boundaries.
Another challenge is the diversity of insider scenarios. Threats range from inadvertent exposure—such as sending confidential files to the wrong recipient—to sophisticated, long-term schemes where employees slowly siphon data. Each scenario has distinct indicators and requires tailored detection and response strategies.
What modern DLP solutions attempt to do
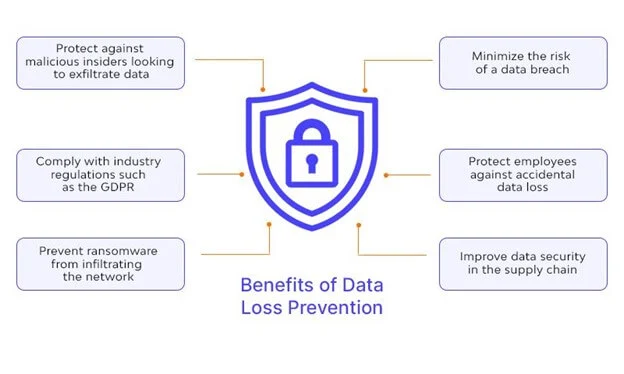
Contemporary DLP platforms aim to monitor, detect, and prevent unauthorized data movement across endpoints, networks, and cloud services. This typically involves content inspection, contextual analysis (who accessed what, when, and how), and enforcement mechanisms like blocking or quarantining transfers. Integration with identity systems and access controls strengthens the ability to correlate events with user behavior.
Many vendors also incorporate machine learning to profile normal user behavior and flag anomalies. Content fingerprinting and classification help pinpoint regulated data — personally identifiable information (PII), financial records, intellectual property — and apply policies automatically. In cloud-first environments, DLP is expected to scan SaaS traffic and enforce controls within applications as well.
Limitations of signature and rule-based DLP
Rule-based engines perform well for known patterns, such as credit card numbers or Social Security numbers, but struggle with unstructured intellectual property or nuanced context. Static rules generate false positives when employees legitimately share information for collaboration, and false negatives when sensitive content is obfuscated or reformatted.
The role and limits of behavioral analytics
Behavioral analytics can reduce noise by focusing on deviations from established baselines. However, defining “normal” is difficult in dynamic workplaces where roles, projects, and toolsets change frequently. High-quality baselines require time and comprehensive telemetry across devices and cloud services, which some organizations lack.
Operational and technical gaps that blunt DLP effectiveness
Several practical factors limit DLP effectiveness beyond the core technology. Coverage gaps are common: BYOD devices, unmanaged cloud instances, and third-party collaboration platforms often sit outside full DLP visibility. Shadow IT accelerates the problem, as employees adopt new tools faster than security teams can integrate them.
Encryption and privileged access present further complications. Encrypted channels and files can hide exfiltration unless endpoint agents or decryption proxies are deployed, which raises privacy and performance concerns. Privileged insiders, such as administrators, can bypass controls if separation of duties and monitoring are insufficient.
Usability and workflow friction
When DLP policies are too strict or poorly calibrated, they impede legitimate work. Frequent false positives frustrate users and lead to workflow circumvention—employees resorting to personal email, USB drives, or unsanctioned cloud accounts to complete tasks. DLP that ignores user experience inadvertently encourages risky behavior.
Alert fatigue and response capacity
Even well-tuned DLP systems produce alerts that require triage. Security teams are often stretched thin and may lack the context to prioritize incidents effectively. Without effective incident response playbooks and automation, important signals can be lost amid routine noise.
Adapting DLP to modern environments
DLP needs to evolve from gatekeeper to orchestrator, integrating with identity, access management, endpoint detection, and cloud security posture tools. Contextual signals — device posture, geolocation, role changes, and external threat intelligence — should feed into DLP decisions. This makes policy enforcement more dynamic and less disruptive to legitimate activities.
Deploying DLP across endpoints, cloud applications, email, and data stores is essential. For cloud-native collaboration tools, native APIs and CASB integration provide deeper visibility than network-based inspection. Endpoint agents remain important for content discovery and enforcement when data leaves managed environments.
Policy engineering and risk-based controls
Policy engineering replaces one-size-fits-all rules with risk-scored controls. Rather than blocking every potential leak, policies can escalate responses based on sensitivity, context, and user risk level—ranging from warnings to multi-factor reauthentication to automated quarantine. Risk-based approaches reduce friction and focus resources where they matter most.
Human-focused controls and awareness
Technology alone cannot eliminate insider risk. Continuous training, clear data-handling policies, and streamlined reporting channels contribute to a culture where mistakes are corrected rather than hidden. Regular reviews of access rights and just-in-time permissions reduce standing privileges that insiders can misuse.
When detection is inevitable: response and remediation
Assume that some level of data leakage will occur. Detection must be paired with rapid investigation and containment. Forensic tools, immutable logs, and session recording for high-risk access help reconstruct incidents. Automated containment—revoking sessions, rolling credentials, or isolating endpoints—minimizes dwell time and impact.
Post-incident analysis should feed back into policy refinement. Identifying root causes—weak controls, insufficient training, or malicious intent—enables targeted remediation, whether that means tightening controls, revising workflows, or pursuing disciplinary action.
Practical recommendations for security leaders
Start with data discovery and classification to know what assets exist and why they matter. Focus DLP efforts on high-value, high-risk data flows rather than attempting blanket coverage. Invest in integrations that bring identity, cloud, and endpoint context into DLP decisions.
Implement risk-based policies that adapt to user roles and context, and prioritize usability to reduce circumvention. Build incident response playbooks that include automated containment and escalate to human analysts only when necessary. Finally, treat insider risk as an organizational issue: combine technical controls with governance, accountability, and ongoing education.
Conclusion: DLP is necessary but not sufficient
Data Loss Prevention remains a critical element of a comprehensive security strategy, but expectations must be realistic. DLP tools can significantly reduce accidental leaks and detect many forms of deliberate exfiltration, yet they are not a panacea. Their effectiveness depends on coverage, context, integration, and the organizational processes that surround them.
Real resilience against insider threats comes from blending technology with smarter policies, adaptive controls, and a culture that minimizes risky shortcuts. When DLP is treated as part of an ecosystem—rather than a standalone fix—its value increases and the organization becomes better positioned to keep pace with evolving insider risks.